Quick Note on Phobos Ransomware
This is a quick note about Phobos ransomware analysis. If you’re interesting, I left materials including the sample, required key file and x64dbg’s comments on the repository here.
A Separate 10-Bytes Key File
Retrieved USN journal on victim system shows that at almost the same time the malicious executable was dropped, there was a text file named k.txt dropped at the same location too. The text file was overwritten and deleted before the malicious process exiting.
This flow exists on program’s entry point as shown below:

If return value from CreateFileA with OPEN_EXISTING option is failed, the program will exit.
Tiny Encryption Algorithm With Custom Packer
Looking closely to function at .text, we can see using of constants which relate to a key schedule constant of Tiny Encryption Algorithm (TEA) such as 0xC6EF3720 and 0x61C88647. I didn’t compare the whole section with the actual implementation of TEA, so there’s a chance that this is TEA or modified version of TEA which utilizing the same constants.

The caller of the above function specifies an address of entry point, an address of .data, a length of data on the text file and its value as parameters, controlled by decrementing over ESI register which holds 0x2625A00. This value embedded in .data segment at 0x2020.

If we put a breakpoint after jne at 0x1437, we could see changes on the .text segment:
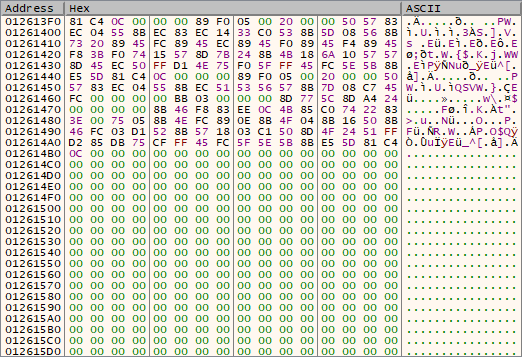

It seems like the 10-bytes is used with TEA to decrypt a garbage data and append to the .text section as a code. I didn’t look further due to access violation exception.
What Does It Look Like In Sandbox?
Not much. The only online sandbox provider that let me specify which submitted files to be executed is ANY.RUN. As you can see here, the process was crashed, and because most of its operation doesn’t rely on Windows API, the sandbox reported exact behavior information when compare to ProcMon.